How to clone USB license keyPosted by Stanley on January 16th, 2020 How to clone USB dongle?
How does dongle work?How a dongle works may be a mystery to some readers. HASP key technology makes use of dedicated microcircuits or microcontrollers that are read-protected. Each key contains a unique operational algorithm. There also has a limited capacity for protected non-volatile memory. Some advanced security keys also are equipped with encryption capabilities by the use of a crypto-processor and a clock. The physical appearance of security keys can vary, but the most common connectivity method is through a USB port. Some dongles connect with LPT or PCMCIA interfaces. Here’s how a hardware security key works. The device is connected to the designated type of computer interface. It then communicates with the software program it is protecting via a dedicated driver and returns data to the application based on its programmed algorithm. If the key provides the proper answer to the apps query, the program continues to operate. If the answer is incorrect, certain functions of the application are disabled or it may be put into a limited demonstration mode. Dongle cloning issuesThere are some high-end USB dongles that provide an option for network management. When this option is employed, the same license can be used by multiple users on a local network. If your team is located in a single room, using this capability makes it unnecessary to have a physical dongle on each machine. You can also run into issues when the application that the dongle is meant to unlock is not supported by your operating system. One way around this problem is to use a virtual machine created with Hyper-V, VirtualBox or VMware. The VM route presents another complication. You now need to find a method of accessing a local USB device from within the virtual environment. How can you clone a dongle USB key and make it available in your VM?
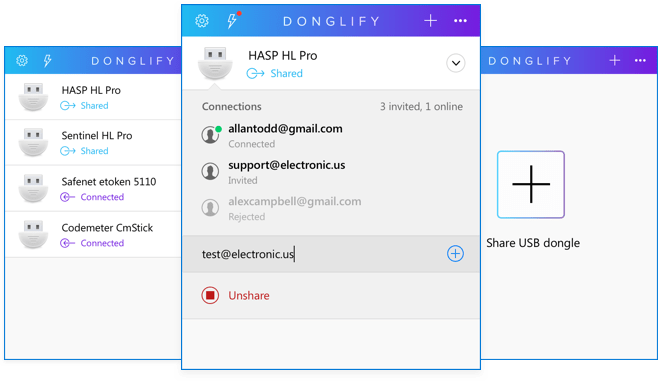
HASP key clone solutionDonglify is an efficient solution to the problem of creating a USB security dongle clone. The tool is available as a dongle clone software and enables you to work with many different dongle keys. It’s really easy to clone a USB dongle with Donglify! It allows you to use the security key across a network and to share its functionality with the remote users regardless of their distance from the actual device. It’s easy to clone a USB dongle using Donglify. It allows you to use the security key across a network, allowing its functionality to be shared with remote users regardless of their distance from the actual device. Here is how to clone a USB license key:
Note that after you clone a USB dongle with Donglify, you can use the device’s virtual copies on multiple remote computers at a time! All you need to do is click “Connect” on every machine that wants to access a shared USB key. Like it? Share it! |